![Cyberthon 2021 Finals - APCDB (pwn)]()
Cyberthon 2021 Finals - APCDB (pwn)
We've found a network service that seems to be posing as a fake directory of APOCALYPSE members…
![confusion bug in ChakraCore]()
confusion bug in ChakraCore
Introduction Chakrazy is a browser CTF challenge created by team PPP for the 2017 PlaidCTF event. It…
![33C3 CTF feuerfuchs challenge]()
33C3 CTF feuerfuchs challenge
Introduction So I've been playing with the browser exploitation recently, by studying some browser…
![MeePwn CTF 2017 -- Brainfuck 1 & 2]()
MeePwn CTF 2017 -- Brainfuck 1 & 2
Category: Pwnable Both binaries are 64 bit ELF, No RELRO, No canary, PIE & NX enabled. Brainfuck1 Th…
![MeePwn CTF 2017 - Old School]()
MeePwn CTF 2017 - Old School
Category: Pwnable 64 bit ELF, Partial RELRO, NX enabled, No PIE, has canary. -------- BookStore ----…
![MeePwn CTF 2017 - anotherarena]()
MeePwn CTF 2017 - anotherarena
Category: Pwnable 64 bit ELF, Partial RELRO, canary & NX enabled, No PIE. The program is a simple…
![DEFCON CTF 2017 Quals - badint]()
DEFCON CTF 2017 Quals - badint
Category: Potent Pwnables 64 bit ELF, Partial RELRO, NX enabled, No canary & PIE. libc not provided.…
![33C3 CTF 2016 - babyfengshui]()
33C3 CTF 2016 - babyfengshui
Category: pwn Points: 150 32 bit ELF, with Partial RELRO, canary & NX enabled, No PIE program menu:…
![33C3 CTF 2016 - ESPR]()
33C3 CTF 2016 - ESPR
Category: pwn Points: 150 This time there's no binary or libc.so provided, only an image looks like…
![SECCON CTF 2016 - checker]()
SECCON CTF 2016 - checker
Category: Exploit Points: 300 64 bit ELF with Full RELRO, stack canary, NX enabled, No PIE. A quick…
![SECCON CTF 2016 - chat]()
SECCON CTF 2016 - chat
Category: Exploit Points: 500 64 bit ELF with Partial RELRO, stack canary & NX enabled, No PIE. The…
![HITCON CTF 2016 Quals - Hackpad]()
HITCON CTF 2016 Quals - Hackpad
Category: Crypto & Forensics Points: 150 I did not look at this challenge at first, until I found…
![HITCON CTF 2016 Quals - ROP]()
HITCON CTF 2016 Quals - ROP
Category: Reverse Points: 250 The challenge gave us a file call rop.iseq. By checking the file…
![HITCON CTF 2016 Quals - Secret Holder]()
HITCON CTF 2016 Quals - Secret Holder
Category: pwn Points: 100 I did not finish the challenge during the contest, but was able to solve…
![HITCON CTF 2016 Quals - Shelling Folder]()
HITCON CTF 2016 Quals - Shelling Folder
Category: pwn Points: 200 64 bit ELF, with all the protection enabled. The program is a simple file…
![HITCON CTF 2016 Quals - flame]()
HITCON CTF 2016 Quals - flame
Category: PPC ( more like Reverse ) Points: 150 We were given a 32 bit PowerPC ELF. Fortunately I've…
ASIS CTF Finals 2016 - car market
Category: pwn Points: 177 64 bit ELF, with Partial RELRO, Canary & NX enabled, no PIE. libc.so was…
![MMA 2nd CTF 2016 - greeting]()
MMA 2nd CTF 2016 - greeting
Category: pwn Points: 150 After a long period of time without playing any CTF, I finally finished my…
![Hackdotlu CTF 2015 - secret library]()
Hackdotlu CTF 2015 - secret library
Category: Reversing Points: 200 64 bit ELF This service is a some kind of weird library system…
![CSAW CTF 2015 - FTP & FTP2]()
CSAW CTF 2015 - FTP & FTP2
Category: Reversing (FTP) & Exploitable (FTP2) Points: 300 (FTP) & 300 (FTP2) 64 bit ELF. It's a…
![CSAW CTF 2015 - Hacking Time]()
CSAW CTF 2015 - Hacking Time
Category: Reversing Points: 200 This challenge gave us a NES ROM. After we launch it with NES…
ASIS CTF 2015 Quals - Saw this (1 & 2)
Category: pwn Points: 100 (Saw this-1), 400 (Saw this-2) Survive and get the flag! Note: This…
![DEFCON CTF 2015 Quals - catwestern]()
DEFCON CTF 2015 Quals - catwestern
Category: Coding Challenge Points: 1 meow catwestern_631d7907670909fc4df2defc13f2057c.quals…
![ASIS CTF 2015 Quals - grids]()
ASIS CTF 2015 Quals - grids
Category: Programming Points: 300 In each stage send the maximun size of area that can be covered…
![DEFCON CTF 2015 Quals - mathwhiz]()
DEFCON CTF 2015 Quals - mathwhiz
Category: Baby's First Points: 1 mathwhiz_c951d46fed68687ad93a84e702800b7a.quals.shallweplayaga.me…
DEFCON CTF 2015 Quals - wibbly wobbly timey wimey
Category: Pwnable Points: 2 Wibbly Wobbly Timey Wimey Don't blink! wwtw…
![VolgaCTF 2015 Quals - math problem]()
VolgaCTF 2015 Quals - math problem
Category: PPC Points: 300 nc mathproblem.2015.volgactf.ru 8888 This problem remind me of HITCON…
![VolgaCTF 2015 Quals - my little pwnie]()
VolgaCTF 2015 Quals - my little pwnie
Category: Pwn Points: 250 Just another pwn task. Break in! nc pwnie.2015.volgactf.ru 7777 my_little…
![BackdoorCTF 2015 - Binary + Misc]()
BackdoorCTF 2015 - Binary + Misc
BackdoorCTF 2015 For me, this is a challenge for CTF beginners. Most of the challenges are easy to…
![0CTF 2015 Quals - (Baby)PolyQuine]()
0CTF 2015 Quals - (Baby)PolyQuine
Different people see different me. But I am always myself. <202.112.26.114:12321> Make the output…
![0CTF 2015 Quals - geo newbie]()
0CTF 2015 Quals - geo newbie
Talentyange gives lots of tedious apks and you know how bad he is now. Let's try some interesting…
![SCTF 2014 - Code400]()
SCTF 2014 - Code400
Code400 gave us a python script import json import hashlib import os import base64 from Crypto…
![SCTF 2014 - Pwn200]()
SCTF 2014 - Pwn200
SCTF is a CTF contest hold by XCTF ( seems like a Chinese version's CTFtime.org ). Teaming up with my labmates, we have a lot of fun solving the challenges, and scored 2161 pts with the final rank 13/659.
![SCTF 2014 - Pwn400]()
SCTF 2014 - Pwn400
Similar with Pwn200, Pwn400 gave us a binary file, but no libc.so. Open it with IDA Pro and analyze it, we found some information:
![ASIS CTF Finals 2014 - TicTac]()
ASIS CTF Finals 2014 - TicTac
Description: Find flag in this file After extracting data in the compressed file, we found a .pcap…
![ASIS CTF Finals 2014 - How much exactly + Lottery]()
ASIS CTF Finals 2014 - How much exactly + Lottery
Both challenges are kind of easy, so I decide to put their writeups together. Description: 4046925:…
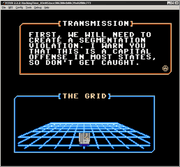
![ASIS CTF Finals 2014 - SATELLITE]()
ASIS CTF Finals 2014 - SATELLITE
Description: Connect here and find the flag: nc asis-ctf.ir 12435 After we connect to the server, it…
![CSAW CTF - Exploitation 200 pybabbies]()
CSAW CTF - Exploitation 200 pybabbies
CSAW CTF 2014 is the second CTF contest I've attended ( the first one was the HITCON CTF 2014 ) . Si…
![CSAW CTF 2014 - Exploitation 400 saturn]()
CSAW CTF 2014 - Exploitation 400 saturn
First the challenge gave us a binary file (ELF for Intel-386). But we can't execute it, cause we don…